PostgreSQL Security Patch Fixes Eleven Vulnerabilities Without Breaking Your Database
The latest PostgreSQL security patch drops for versions fourteen through eighteen, and it actually fixes eleven real vulnerabilities instead of just bumping version numbers. This update addresses memory corruption bugs, SQL injection vectors in replication tools, and a sneaky timing leak that could expose MD5 passwords. Operators will want to apply this release before attackers start testing the integer wraparound flaws that have been sitting in the codebase for months.
Why This PostgreSQL Security Patch Matters More Than Usual
Most minor releases just clean up edge cases and update timezone files, but this one actually touches the authentication layer and replication commands that database administrators rely on daily. The integer wraparound flaw in server allocations is particularly nasty because it lets crafted application inputs trigger out of bounds writes that crash the backend process. Operators frequently notice similar undersizing bugs cause silent data corruption during heavy batch loads before they get patched, so treating this as a priority update makes sense. The SQL injection holes in pg_createsubscriber and REFRESH PUBLICATION also stand out since logical replication setups often run with elevated privileges by default.
How to Apply the PostgreSQL Security Patch Without Downtime
Database administrators do not need to dump and reload their databases or run pg_upgrade for this release since all minor updates are fully cumulative. Dumping and reloading data just to apply a minor version bump is a waste of time that only slows down maintenance windows. The standard procedure involves stopping the postgres service, replacing the binaries with the new files, and restarting the daemon. This works because PostgreSQL stores its data directory in a format that stays backward compatible across minor versions, so swapping executables is safe as long as the operating system architecture matches perfectly. If an environment still runs version fourteen, planning an upgrade path becomes mandatory since official support ends on November twelfth twenty twenty six. Running an unsupported database through next year leaves systems exposed to unpatched memory leaks and authentication bypasses that inevitably surface in public exploit databases.
What the Sixty Bug Fixes Actually Change for Your Workloads
Beyond the security holes, this release quietly fixes several planner and replication quirks that cause headaches during routine maintenance. The foreign key deferrability loss bug meant that constraints marked as deferred would suddenly behave like immediate checks after toggling enforcement status, which breaks application transaction logic without throwing obvious errors. Partition pruning improvements in the query planner will likely speed up large analytical queries that filter on range columns, while the fix for array_agg parallel execution prevents duplicate or missing rows during heavy concurrent workloads. The timezone data update to release twenty twenty six b also handles permanent daylight saving time changes in British Columbia and corrects historical transition dates for Moldova, which matters if applications log timestamps across multiple regions.
Which Vulnerabilities Actually Require Immediate Attention
The memory disclosure flaw in the timeofday function and the SSL negotiation recursion issue both allow local attackers to trigger denial of service or leak server memory through crafted timezone zones. Remote exploitation remains limited since most flaws require existing database access, but the libpq stack overflow in lo_export functions stays dangerous for applications that dump large binary objects directly into client buffers. The refint module buffer overflow and SQL injection vectors concern administrators because they let unprivileged users escalate to operating system level execution through cascade primary key updates. Teams should verify that replication tools use subscription names generated internally rather than accepting raw user input, since the pg_createsubscriber command parses those strings directly into SQL statements.
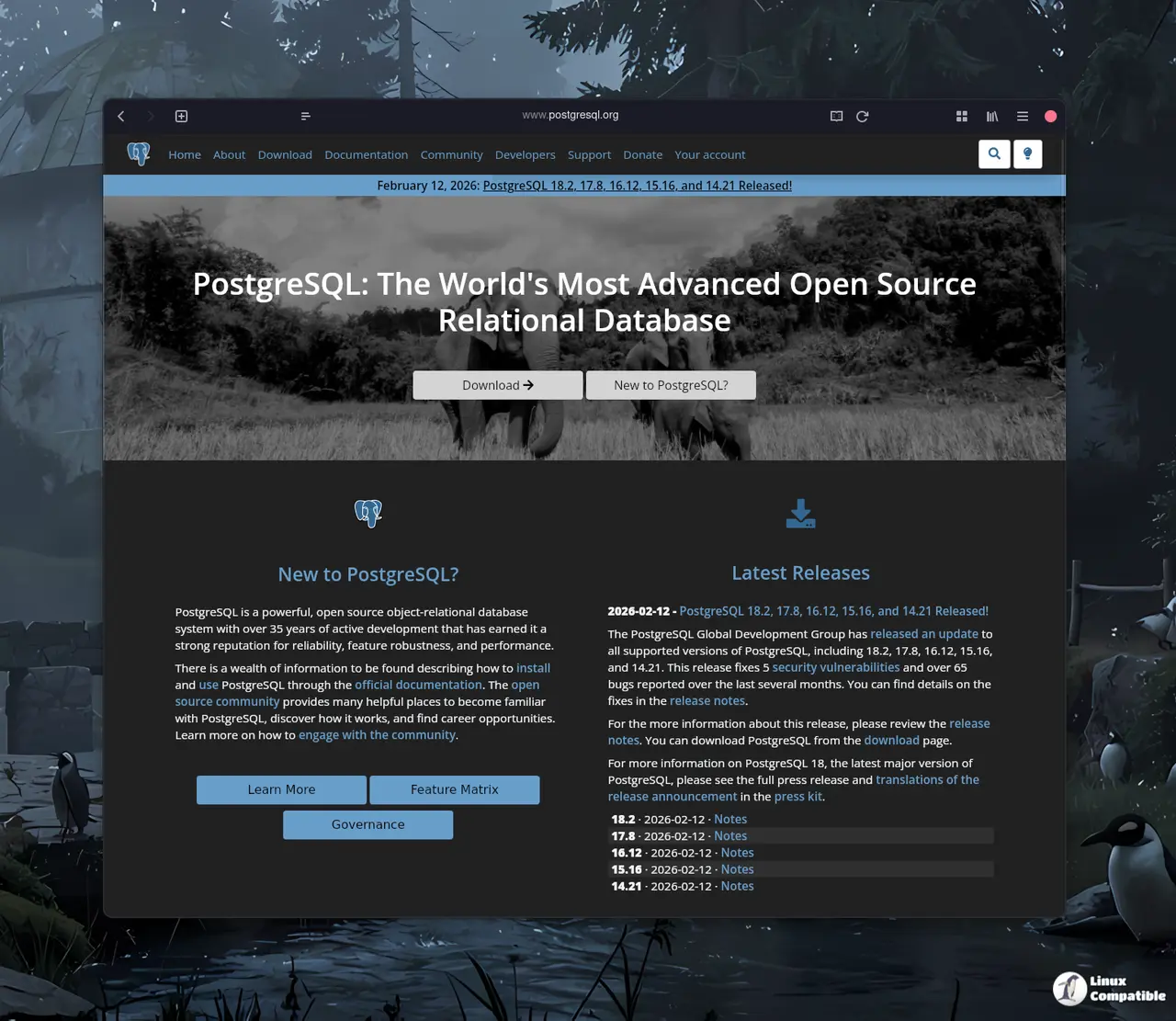
Grab the binaries from the official download page and run a quick version check after restart to confirm the patch landed correctly. Let me know if the replication setup throws any weird errors during the upgrade window.