Ondřej Surý has pushed a comprehensive set of PHP security updates to the Sury repository, patching critical vulnerabilities across every supported branch from version 5.6 through 8.5.6. These releases specifically target Debian GNU/Linux 11 (Bullseye) LTS, 12 (Bookworm), and 13 (Trixie), ensuring both modern stacks and legacy applications receive essential fixes for issues like cross-site scripting, memory corruption, and SQL injection. Administrators can quickly apply the patches by adding the official repository key, updating their package index, and running a standard system upgrade without risking version mismatches across different Debian releases. Keeping these backported updates current is the most reliable way to protect production servers until legacy frameworks are fully migrated to actively supported branches.
How to Apply the PHP Security Updates Debian Systems Need Right Now
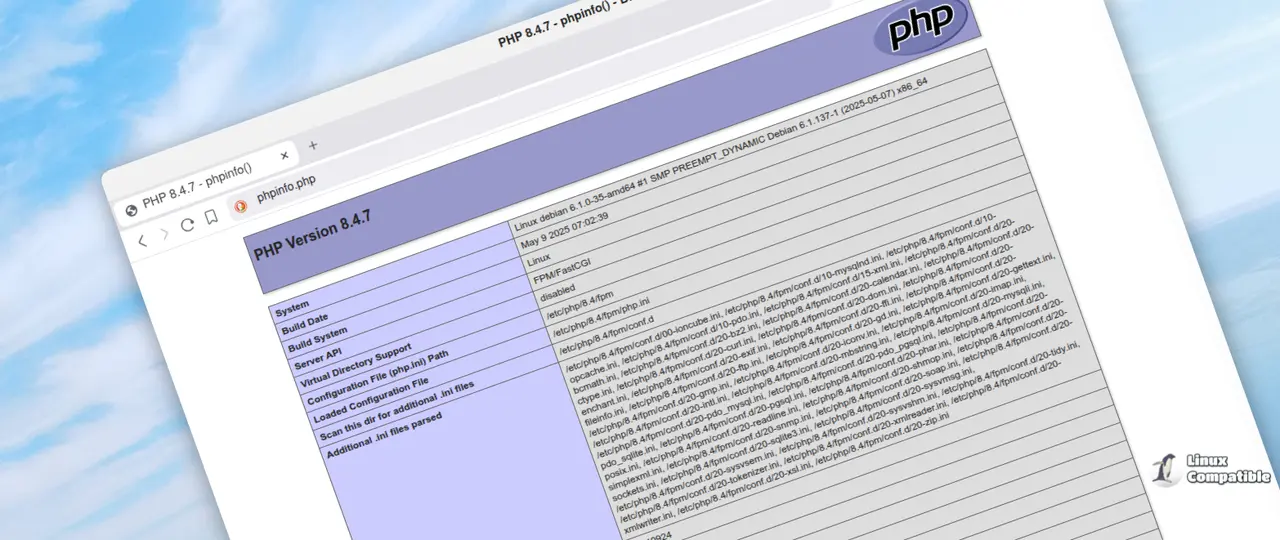
The latest batch of PHP Security Updates Debian administrators rely on just landed in the Sury repository, and skipping them leaves servers wide open to known exploits. These releases patch critical vulnerabilities across every supported branch from five point six through eight point five six for Debian GNU/Linux 11 (Bullseye) LTS, 12 (Bookworm), and 13 (Trixie). Getting these installed requires a few straightforward commands, but the payoff is keeping production environments from getting pwned by automated scanners that already have scripts ready to go.
What Actually Changed This Time
The most pressing fixes target the FastCGI Process Manager and multibyte string handling. A cross-site scripting vulnerability in the FPM status endpoint could leak sensitive request data to anyone who knows the URL. The multibyte string extension also had a null pointer dereference that triggers when malformed input reaches mb_ereg_search_init. Server administrators have watched production environments crash when developers pass unvalidated strings directly into regex functions without checking encoding boundaries, and this patch closes that exact gap. PDO_Firebird received an SQL injection fix for NUL bytes in quoted strings, which matters because legacy applications still rely on Firebird for financial or inventory tracking. The SOAP extension got three separate memory management patches that prevent use after free errors when Apache maps fail to parse headers correctly. Standard library functions also fixed a signed integer overflow that could corrupt character array offsets during string manipulation. These are not theoretical edge cases. They show up in real traffic logs when poorly written plugins or custom scripts mishandle user input, and the patched binaries stop those crashes before they become full system compromises.
How to Install the PHP Security Updates Debian
Adding the repository requires root privileges and a few standard package management tools. The first step installs apt transport https, lsb release, ca certificates, and curl because modern Debian systems need these to verify secure connections and identify the correct release codename. Downloading the GPG key from packages.sury.org ensures that apt trusts the incoming PHP packages instead of rejecting them as unsigned. Writing the repository line into sources list d creates a dedicated file so system updates do not accidentally overwrite custom package sources. Running apt update refreshes the local package index so the system recognizes the new security patches. Finally, upgrading php fpm or php cli pulls in the corrected binaries without touching unrelated software. The Sury repository currently ships PHP 8.2.31, 8.3.31, 8.4.21, and 8.5.6 for Debian GNU/Linux 11 (Bullseye) LTS, 12 (Bookworm), and 13 (Trixie). Older branches like 7.4 and 8.0 still receive backported security fixes through the same setup, which keeps legacy stacks from rotting in place.
#!/bin/bash # To add this repository please do:
if [ "$(whoami)" != "root" ]; then
SUDO=sudo
fi
${SUDO} apt-get -y install apt-transport-https lsb-release ca-certificates curl
${SUDO} wget -O /etc/apt/trusted.gpg.d/php.gpg https://packages.sury.org/php/apt.gpg
${SUDO} sh -c 'echo "deb https://packages.sury.org/php/ $(lsb_release -sc) main" > /etc/apt/sources.list.d/php.list'
${SUDO} apt-get update
Version Coverage and Legacy Support
Ondřej Surý has maintained PHP packages for Debian since version 5, which means these builds match official upstream releases while adding distribution specific hardening. The current release covers everything from the long deprecated eight point two branch up to eight point five six, giving administrators flexibility depending on application requirements. Supporting older versions requires backporting security fixes that never made it into stable upstream branches, so the Sury repository essentially acts as a bridge between abandoned code and modern threat landscapes. Developers running legacy frameworks should verify compatibility before upgrading, since some third party libraries still depend on deprecated functions that get quietly removed in newer minor releases. Keeping an old PHP version patched is better than leaving it completely unattended, but migrating to a supported branch remains the only real long term fix. The repository structure keeps each Debian release isolated, so Bullseye users will not accidentally pull Bookworm binaries when running apt upgrade. Administrators managing older stacks should note that the Sury repository also provides PHP 5.6.40-95, 7.0.33-86, 7.1.33-74, 7.2.34-61, 7.3.33-30, 7.4.33-26, 8.0.30-20, and 8.1.34-3. Those exact build numbers reflect the Debian packaging convention where the upstream version is followed by a distribution release counter, so package managers can track incremental security backports without breaking dependency chains.
Reporting Issues and Tracking Changes
Bug tracking moved to a public Codeberg instance because email inboxes tend to accumulate unread messages faster than maintainers can process them. Submitting reports through the web interface ensures that patches get assigned properly and that duplicate issues do not clutter development workflows. The official wiki hosts installation guides and configuration examples, so users who need help with PHP FPM pools or opcache tuning should check there before opening support tickets. Keeping an eye on release notes helps administrators anticipate breaking changes before they hit production servers.