Mutt 2.3.2 Released With Critical GPGME and IMAP Fixes
The latest update for the terminal email client brings a handful of stability patches that actually matter to people who run their mail through command line tools. Mutt 2.3.2 drops today with fixes for segmentation faults, infinite loops, and authentication quirks that could quietly break your workflow. Users should grab the tarball soon and verify the signature before compiling or installing anything.
Why This Update Matters For Terminal Mail Users
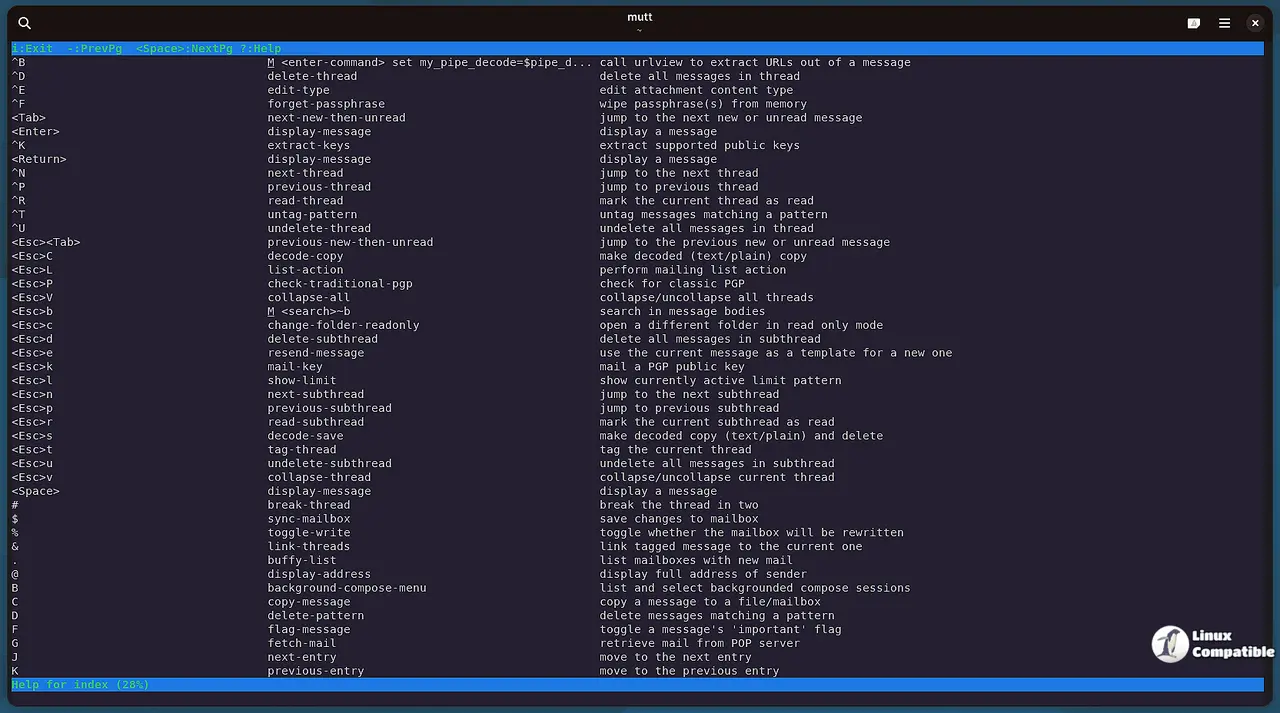
Running a text based email client means dealing with low level protocol details that graphical apps usually hide behind layers of abstraction. The GPGME segmentation fault fix addresses a crash that could happen during encryption operations, which is exactly the kind of silent failure that makes people question their sanity when debugging message streams. The infinite loop patch in data_object_to_stream() prevents the application from hanging indefinitely when processing certain attachments or encrypted blocks. Those two changes alone justify the update for anyone who relies on Mutt for daily mail handling instead of waiting for a graphical client to freeze during a routine check.
Authentication And Protocol Adjustments
Several IMAP related patches clean up how credentials and security levels are handled during connection setup. The auth_cram MD5 digest fix swaps a risky memory operation for memcpy, which stops potential data corruption when storing secrets in temporary buffers. A similar adjustment to imap_auth_gss() corrects the buffer size type and validates the security level check before proceeding with the handshake. These changes might sound like developer housekeeping, but they directly impact how reliably the client authenticates against modern mail servers that enforce strict protocol compliance and reject malformed packets.
Key Verification And Installation Notes
The maintainer updated an expired public key, which means users who previously imported the signature file will likely see a warning about an outdated certificate. Refreshing the local keyring or reimporting the key from the official sources resolves the notice without breaking existing configurations. Anyone planning to compile from source should download the tarball directly from the project server and verify the detached signature before running make. Skipping this step leaves the build process open to tampered archives, which defeats the purpose of using a well maintained open source tool in the first place. The verification command itself is straightforward, but it forces users to acknowledge that trust must be established manually when working outside of package manager sandboxes.
The terminal email space stays niche for a reason, but updates like this keep it from falling apart at the seams. Grab the release when you have a spare moment and let the client handle your inbox without throwing unexpected errors.