Tails 7.7.3 Drops Emergency Kernel Fix to Stop Privilege Escalation Attacks
Tails 7.7.3 just hit the servers as an emergency patch for a critical Linux kernel flaw that could hand attackers full control of your system. The update closes Dirty Frag, patches Tor Browser and the client software, and bumps Thunderbird to keep privacy tools from leaking identity data. Anyone running this live operating system should grab the new ISO or push the upgrade immediately before unpatched versions become an easy target.
Why This Emergency Patch Actually Matters
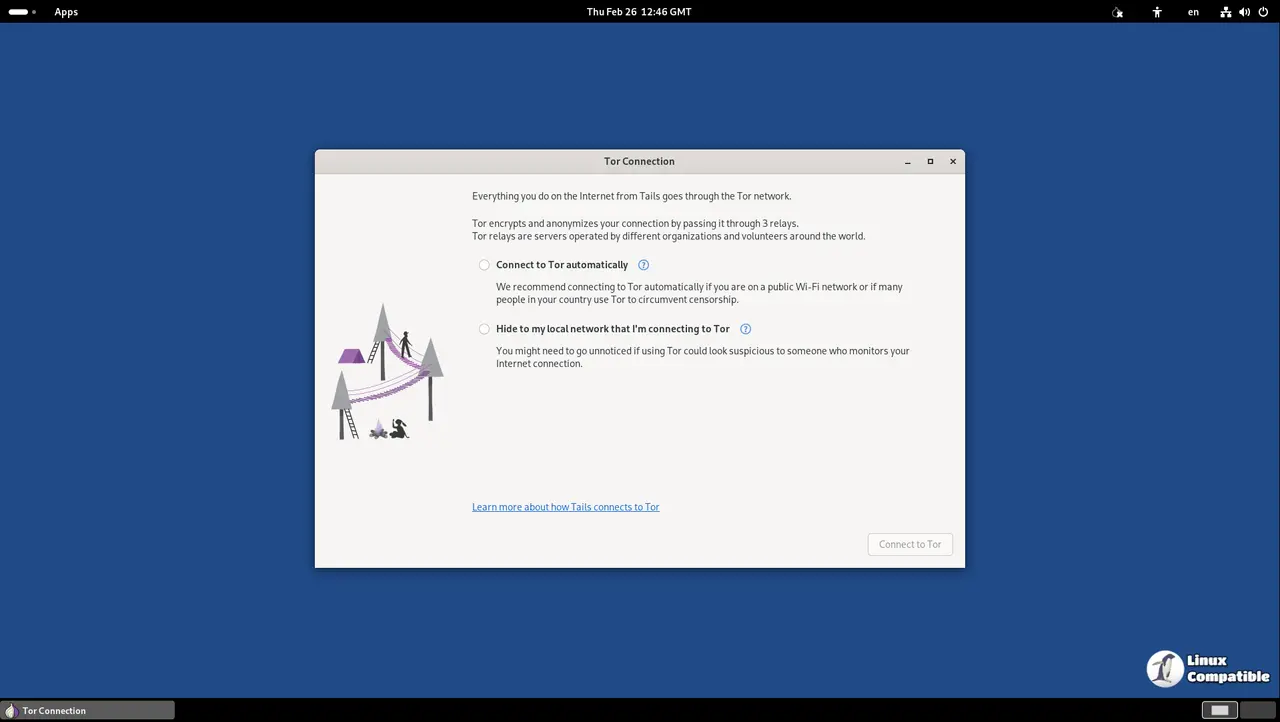
The Dirty Frag vulnerability sits in the Linux kernel and works by letting a regular application slip past sandbox restrictions to grab root access. Tails developers noted that an attacker could chain this with other flaws, like Copy Fail, to completely hijack the session and deanonymize users. Security teams rarely call out specific exploit chains unless they expect them to be weaponized soon. The fact that this release exists as an emergency build means the kernel flaw crosses into high risk territory. Running older versions on a USB stick or virtual machine leaves systems exposed until the patch lands.
What Gets Updated in This Release
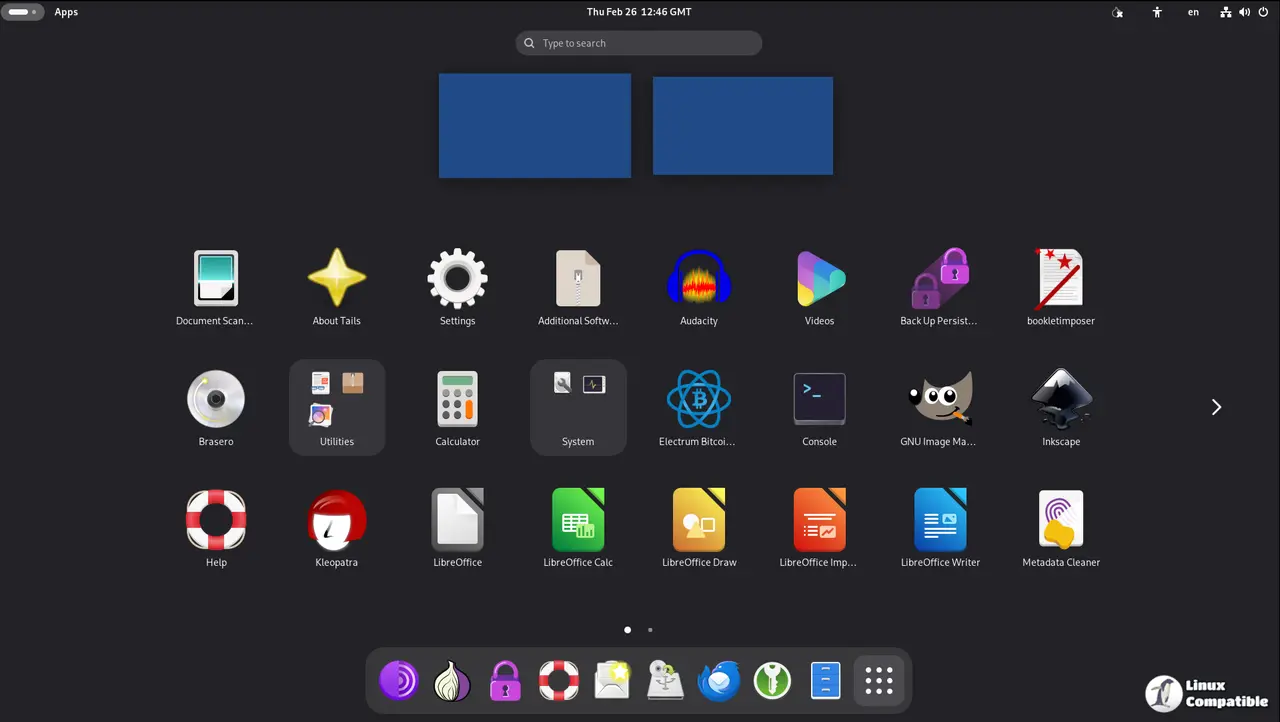
Tor Browser moves to version 15.0.12, which pulls in Firefox ESR 140.10.2 and closes browser side vulnerabilities that could track or fingerprint users. The underlying Tor client upgrades to 0.4.9.8 to fix protocol level bugs that might leak circuit information. Thunderbird gets bumped to 140.10.1, which keeps email clients from falling behind on security patches while handling encrypted messages. Firmware files refresh to the April 2026 snapshot, and the automated test suite shifts to a newer QEMU machine configuration to catch regressions before they hit stable builds.
How to Apply Tails 7.7.3 Safely
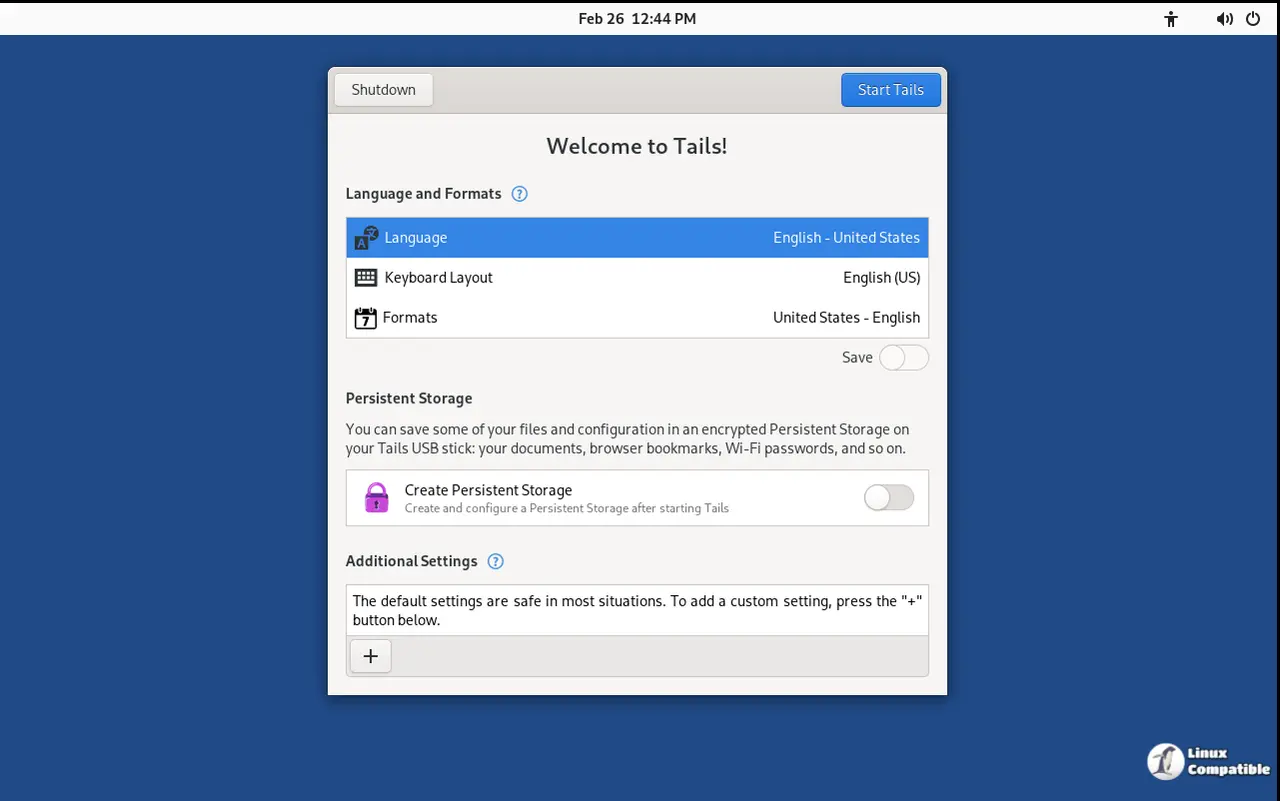
Users with persistent storage enabled should back up encrypted documents first since the upgrade process rewrites system partitions. The live USB installer handles the patch automatically when booted from a fresh medium, but machines running older ISOs need the full download to replace the existing environment. Virtual machine users can swap the disk image through the standard Tails installer without touching host configurations. Skipping manual package tweaks is pointless since the hardened security profile breaks easily when third party drivers interfere with Tor circuit routing. Admins who keep this OS running in nested virtualization for testing often forget that the live environment overwrites itself on reboot, which means the patch only sticks after a full ISO replacement.
Grab the update, verify the checksum, and keep those circuits clean.