Tails 7.7.2 Drops to Patch a Critical Kernel Flaw Before It Becomes a Problem
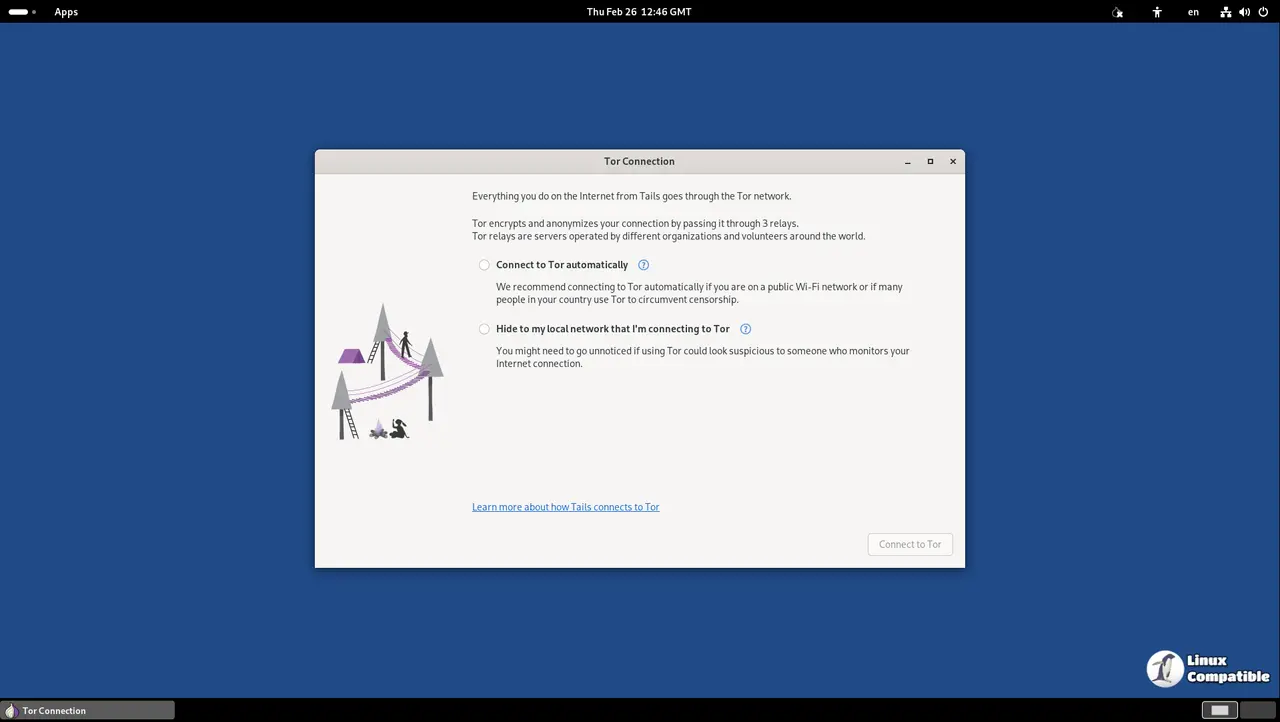
Tails 7.7.2 arrives as an emergency update to close a serious security hole in the Linux kernel that could hand attackers full control of your system. The release bumps the kernel to version 6.12.85 and specifically targets the Copy Fail vulnerability, which lets malicious code escalate privileges if it slips past other defenses. Anyone running Tails should grab this patch immediately since deanonymization risks are too high to ignore.
What the Copy Fail Flaw Actually Does
The kernel update addresses a privilege escalation bug that follows a pretty straightforward attack path once you strip away the jargon. If an attacker manages to trigger another weakness in one of Tails bundled applications, they can chain it with Copy Fail to jump straight into administrator territory. That level of access means they could read stored keys, modify system settings, or route traffic through malicious endpoints to break anonymity. Operators who manage multiple privacy setups often watch threat actors test chained exploits in controlled environments before releasing them publicly, and emergency patches exist precisely because zero day researchers race ahead of official disclosures. The developers note that no active exploitation has surfaced yet, but waiting for a public proof of concept is never a smart move when the attack chain already exists on paper.
How to Apply Tails 7.7.2 Safely
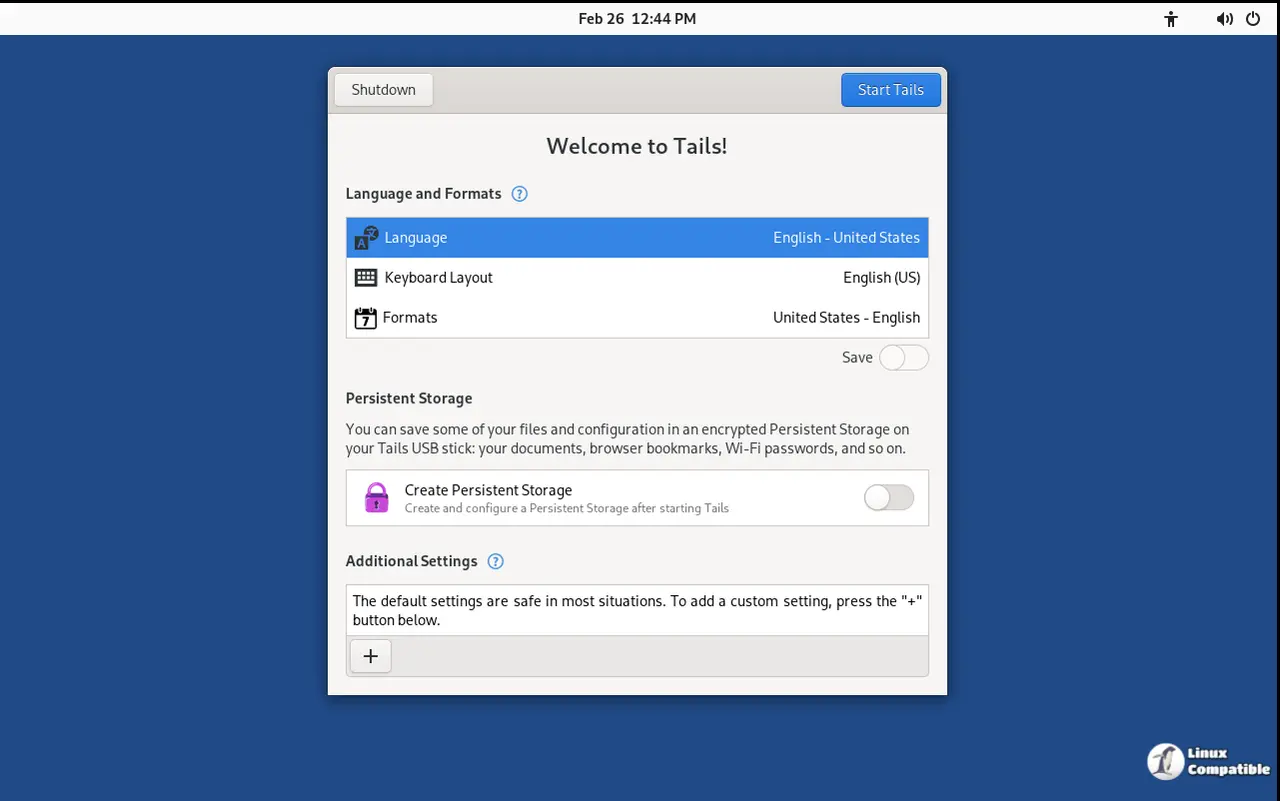
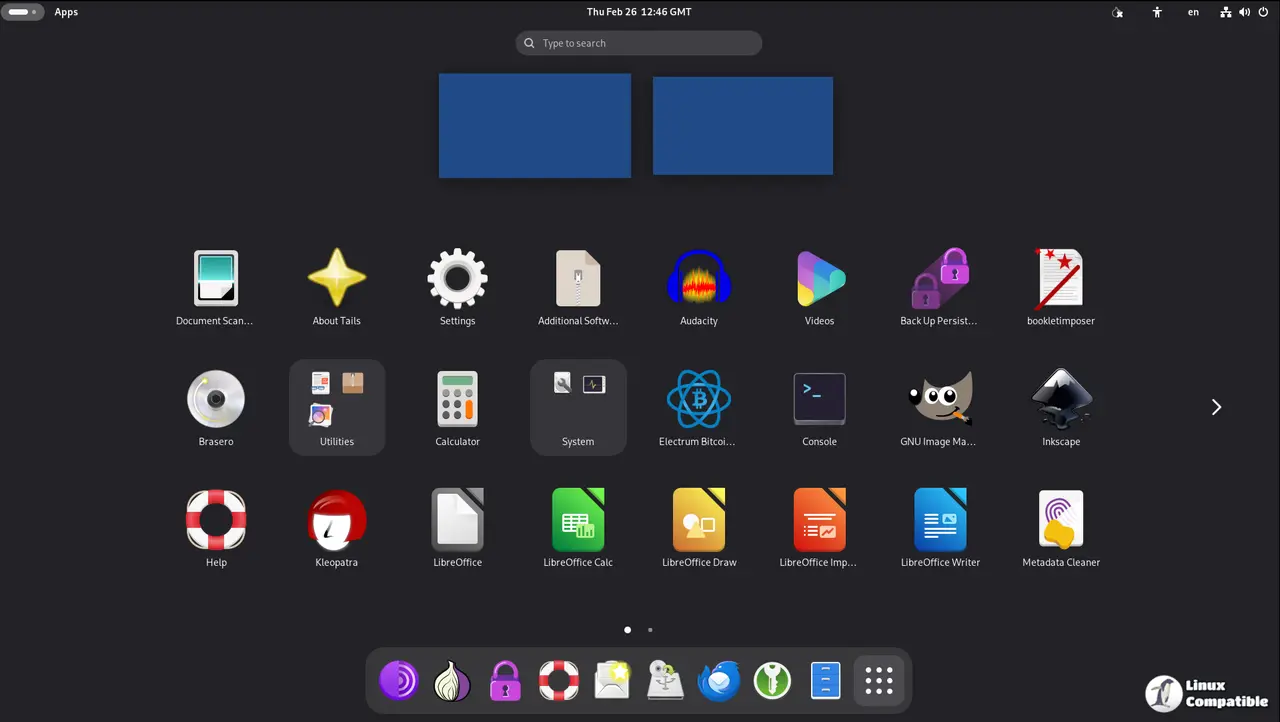
Getting this version onto a machine requires downloading the fresh ISO and verifying its signature before flashing it to a USB drive. The verification step matters because tampered installers could introduce backdoors right at the start of the process, completely bypassing the anonymity guarantees that make the distro useful in the first place. Users should check the detached signature file against the official release notes, then use a trusted imaging tool like balenaEtcher or Rufus to write the image to a clean drive. Once booted, the system will run entirely from memory without touching the host hard drive, which keeps the patch isolated from any existing malware and ensures the kernel update actually takes effect on every boot cycle.
What Changed Under the Hood
Beyond the kernel bump to 6.12.85, the release bundles routine maintenance fixes that tighten overall system stability. The developers addressed several application crashes and updated dependency libraries to match current security standards. Those background adjustments rarely make headlines but they reduce the attack surface by closing outdated code paths that older software tends to exploit. Anyone who relies on Tails for sensitive communications or investigative work will notice smoother performance after applying this version, since memory leaks and driver timeouts tend to compound during long anonymous sessions. The changelog contains the full technical breakdown for those who want to audit every modified file before trusting the build.
Keep the USB drive handy and verify that signature before you boot. The anonymity stack only works when every layer stays patched. Stay safe out there.