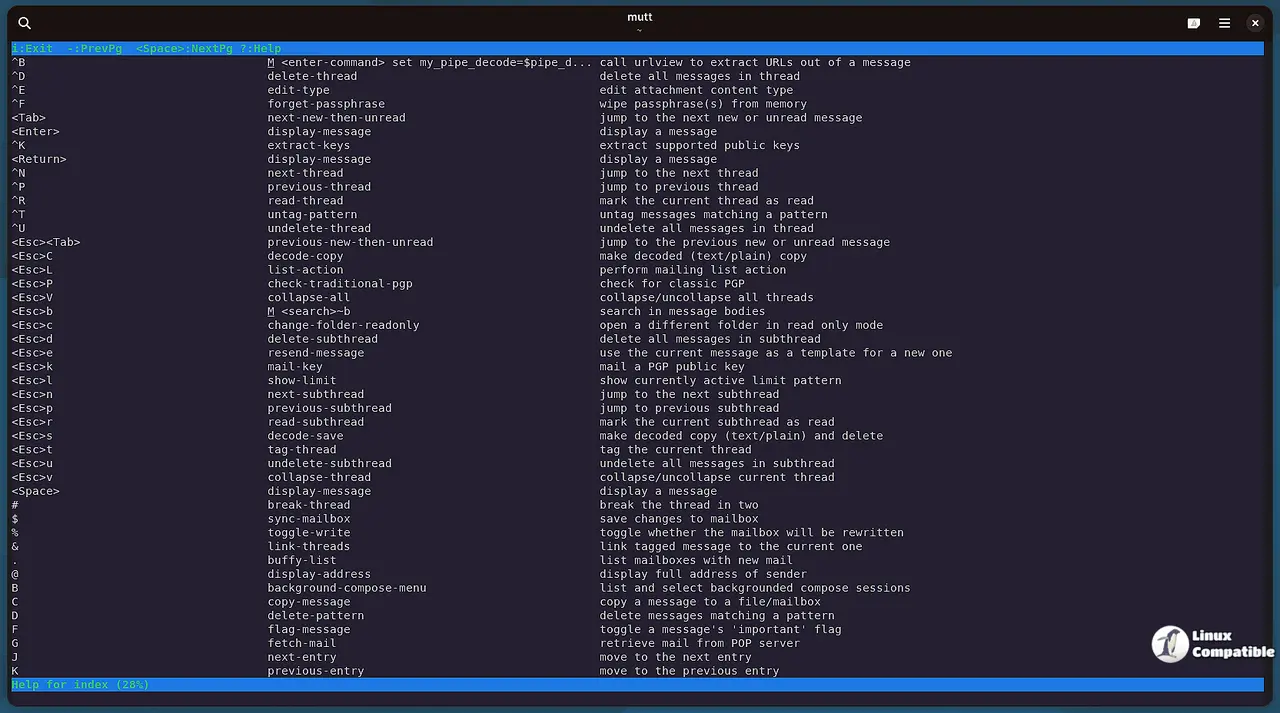
Mutt 2.3.1 Release Fixes Compilation Errors and Refreshes Security Keys
The maintainers have pushed out version 2.3.1 of the Mutt email client to address specific stability issues. Users compiling from source need to know about configuration changes coming in future versions. This update also requires a quick refresh on your GPG keyring to stop verification warnings.
Mutt 2.3.1 Bug Fixes and Configuration Changes
The release notes highlight a fix for a compilation error when configured without wc funcs. This specific flag was often used by older build scripts that assumed standard library behavior. A potential bug in the folder browser also gets addressed, which is crucial for people navigating large mail directories. There are warnings about const strings on bleeding edge distros due to glibc improvements. The team has cleaned up most of these in the master branch but packagers should check the new README file regarding OpenSSL and LibreSSL differences.
Security Updates and Key Expiration Warnings
Kevin, the maintainer, renewed his GPG key expiration date recently. Users who rely on signature verification will see warnings if they do not refresh their keyring periodically. It is easy to dismiss these alerts but re-importing from the official sources prevents future build failures. The option to disable wc funcs will be deprecated in version 2.4.0 and removed later. Anyone depending on that flag should contact the mailing list before the change locks them out of new features.
Stay safe with your email setup.